51![SANS Cyber Threat Intelligence Summit Recent Threat Trend Analysis Scott Montgomery VP, CTO Public Sector [removed] SANS Cyber Threat Intelligence Summit Recent Threat Trend Analysis Scott Montgomery VP, CTO Public Sector [removed]](https://www.pdfsearch.io/img/e2bbee30a57d3733aa0ed2daf1ba5448.jpg) | Add to Reading ListSource URL: digital-forensics.sans.orgLanguage: English - Date: 2014-02-18 18:51:46
|
|---|
52![THE DOLLARS AND “SENSE” BEHIND THREAT INTELLIGENCE SHARING[removed] © Cyber Squared Inc[removed] THE DOLLARS AND “SENSE” BEHIND THREAT INTELLIGENCE SHARING[removed] © Cyber Squared Inc[removed]](https://www.pdfsearch.io/img/418b71d425dff4be399da78ec8b00481.jpg) | Add to Reading ListSource URL: digital-forensics.sans.orgLanguage: English - Date: 2014-02-18 18:53:34
|
|---|
53 | Add to Reading ListSource URL: www.boozallen.comLanguage: English - Date: 2015-01-09 00:35:01
|
|---|
54![Ms. Diane Honeycutt National Institute of Standards and Technology 100 Bureau Drive, Stop 8930 Gaithersburg, MD[removed]Thursday, October 9, 2014 Ms. Diane Honeycutt National Institute of Standards and Technology 100 Bureau Drive, Stop 8930 Gaithersburg, MD[removed]Thursday, October 9, 2014](https://www.pdfsearch.io/img/3c3817eaf345ddf2431664d00cb3b5f6.jpg) | Add to Reading ListSource URL: csrc.nist.govLanguage: English - Date: 2014-10-23 14:08:46
|
|---|
55 | Add to Reading ListSource URL: msisac.cisecurity.orgLanguage: English - Date: 2011-12-15 08:46:44
|
|---|
56 | Add to Reading ListSource URL: www.cert.gov.auLanguage: English - Date: 2014-12-09 20:51:00
|
|---|
57 | Add to Reading ListSource URL: www.datastax.comLanguage: English - Date: 2014-08-13 17:36:55
|
|---|
58 | Add to Reading ListSource URL: www.checkpoint.comLanguage: English - Date: 2014-07-22 16:23:21
|
|---|
59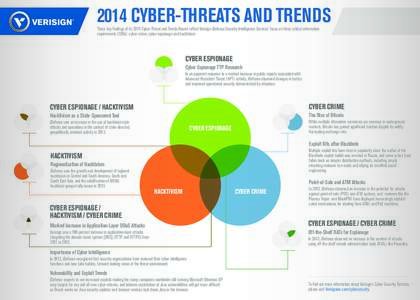 | Add to Reading ListSource URL: www.verisigninc.comLanguage: English - Date: 2014-07-18 15:15:04
|
|---|
60 | Add to Reading ListSource URL: www.kpmg.comLanguage: English |
|---|